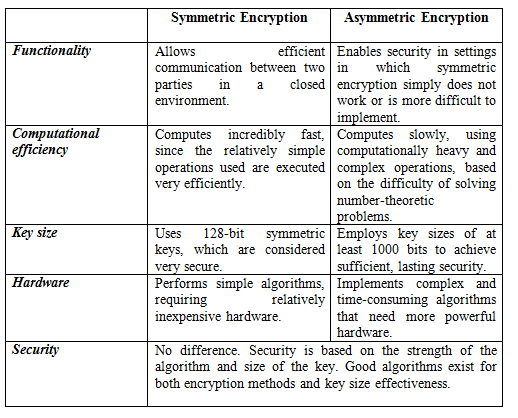
The principal aspects of the two encryption methods ( symmetric and Asymmetric key) are compared in the table below ( Reference Mohamed Abomhara, Khalifa, Othman Zakaria Omar, Zaidan A. A, Zaidan B. B. and Alanazi, Hamdan O. (2010), Journal of Applied Sciences))
Wednesday, 29 August 2012
Using symmetric key algorithms to secure online video streaming
Symmetric keys can provide
confidentiality but they cannot perform authentication, because there is no way
to prove through cryptography who had actually sent a message if two people are
using the same key. The following are the advantage and disadvantage of
using symmetric key systems to secure the online video streaming:
Advantages
- It is much faster than asymmetric key
systems.
- Its security is dependent on the length of
the key. With a large key size, the algorithm will be harder to break,
because symmetric algorithms carry out relatively simplistic mathematical
functions on the bits during the encryption and decryption processes.
- It does not require much computing power.
Disadvantages
- It requires a secure mechanism to deliver the
keys.
- Each pair of users needs a unique key; if
a user has N people to contact, then N secret keys must be maintained so
that as the number of individuals increases, so does the number of keys.
- Management of the symmetric keys can be problematic.
- Provides confidentiality but cannot authenticate, because the secret key is shared.
Tuesday, 21 August 2012
An Overview of the suitability of using symmetric key to secure multimedia data
With the increasing and continuous use of digital communications on the internet in recent times, security is becoming more and more relevant and important. However, special and reliable security is required for the many digital applications available such as video conferencing, digital television and mobile TV. The classical techniques of data security are not appropriate for the current multimedia usage. This study addresses the current algorithm of multimedia encryption schemes that have been proposed in the literature and description of multimedia security. It is a comparative study between symmetric key encryption and asymmetric key encryption in achieving an efficient, flexible and secure video data.( Mohamed Abomhara, Khalifa, Othman Zakaria Omar, Zaidan A. A, Zaidan B. B. and Alanazi, Hamdan O. (2010), Journal of Applied Sciences). ( http://irep.iium.edu.my/5618/).
A review on multimedia communications cryptography
Now-a-days, Due to the repaid increasing and continuous use of
multimedia communications on the internet, Security is becoming more and more
relevant and important. However, special and reliable security is required for
the many multimedia applications available such as video conferencing, digital
television and mobile TV. The classical techniques of data security are not
appropriate for the current multimedia usage. This study will presents the
currently algorithm of multimedia encryption schemes that have been proposed in
the literature and description the effectiveness of the multimedia security. It
is a comparative study between symmetric key encryption and asymmetric key
encryption in achieving an efficient, flexible and secure video data.
(Salem, Yasser, Mohamed Abomhara , Khalifa, Othman, Omer Zaidan, Aos Alaa Zaidan, and Bilal Bahaa (2011), Research Journal of Information Technology) ( http://irep.iium.edu.my/2241/).
(Salem, Yasser, Mohamed Abomhara , Khalifa, Othman, Omer Zaidan, Aos Alaa Zaidan, and Bilal Bahaa (2011), Research Journal of Information Technology) ( http://irep.iium.edu.my/2241/).
Subscribe to:
Posts (Atom)